Slate: Certified Data Sanitisation Platform
A hardware appliance and bootable software platform that sanitises any storage media to the standards that defence, government, and enterprise auditors require, with tamper-evident certificates and zero cloud dependency.
<90s
256GB NVMe wipe + verify
4
Simultaneous drives
-80%
Cost vs. external vendor
6
Compliance standards
0
Cloud dependency (air-gapped)
The Problem
Every organisation that handles sensitive data eventually needs to sanitise storage media. Drives get decommissioned, laptops get returned at end of lease, servers get retired, classified systems get dismantled. The data on those drives needs to be irrecoverably destroyed to a standard that satisfies auditors.
The standards are unambiguous. NIST 800-88 Rev 1 defines Clear, Purge, and Destroy methods for different media types and sensitivity levels. The Australian Government ISM mandates specific sanitisation controls. ASD publishes media destruction guidelines that defence and intelligence agencies must follow. These aren't optional. Non-compliance is an audit finding, a security incident, or worse.
Most organisations handle data sanitisation badly. The options are grim: pay an external vendor $15-50 per drive (expensive, slow, no real-time visibility), use free tools like DBAN that produce no audit trail (non-compliant), or trust an intern with a USB stick and a prayer.
Defence and government organisations face a harder version of this. Classified media can't leave the facility. Air-gapped environments can't upload certificates to the cloud. And every sanitisation event needs to be tied to an authenticated operator with a tamper-evident record that survives audit scrutiny.
What We Built
Slate is a complete data sanitisation platform in two form factors, a dedicated hardware appliance and a bootable software image, backed by a cloud certificate management portal. It handles every media type, meets every relevant standard, and works in both connected and air-gapped environments.
The design philosophy: make the right thing the easy thing. Operators don't need to know which sanitisation method to use. Slate detects the drive type and selects the appropriate method automatically. They don't need to remember to generate a certificate, because it happens on every wipe. They don't need to manually enter drive details: the barcode scanner links physical assets to digital records in one tap.
We built this because no existing product covered the full matrix: all media types × all standards × both environments × tamper-evident audit × ease of use. Enterprise tools were expensive and complex. Open-source tools were capable but produced nothing an auditor would accept. Slate sits in the gap.
Two Form Factors, One Engine
The same sanitisation engine and compliance logic powers both form factors. The Appliance is for dedicated sanitisation operations. Boot is for wiping machines in place.
Slate Appliance
Dedicated hardware unit. Rugged aluminium enclosure with universal media bays.
Best for
- Dedicated sanitisation stations
- IT asset disposal operations
- Classified environments (air-gapped)
- High-throughput batch processing
Slate Boot
Bootable Linux environment via USB or PXE. Turns any x86 machine into a sanitisation station.
Best for
- End-of-lease laptop fleets
- Workstation redeployment
- Server decommissioning
- In-place wipe without drive removal

Appliance Hardware
The Slate Appliance packs a serious amount of capability into a compact, rugged unit. The RK3588 SoC provides more than enough processing power for concurrent sanitisation operations, while the peripheral ecosystem handles the full operator workflow, from authentication to labelling.
Processing
Media Interfaces
Peripherals
Connectivity
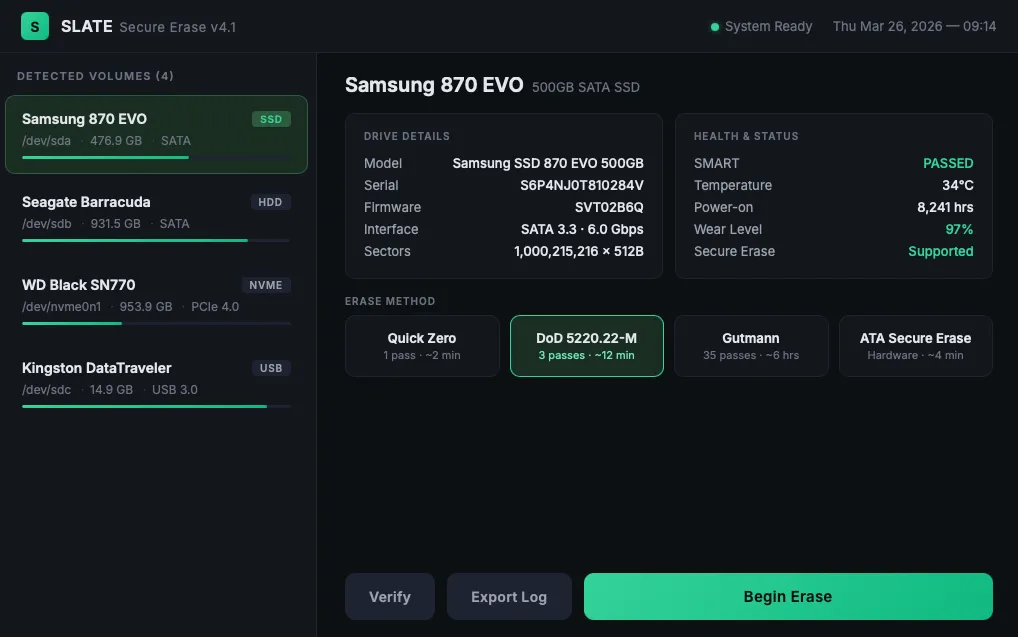
Automatic Method Selection
Different media types require different sanitisation methods. You can't overwrite an NVMe SSD the same way you overwrite a spinning hard drive. The wear-levelling controller and over-provisioned NAND mean a block-level overwrite may not reach every physical cell. NVMe Format with cryptographic erase is the correct approach.
Slate handles this automatically. When a drive is connected, the system identifies the interface type, queries the drive's capability set, and selects the most effective sanitisation method that meets the configured compliance level. Operators see a clear confirmation of what will happen before it starts, but they don't need to make the technical decision themselves.
Every method concludes with a full verification pass: a block-level read of the entire drive to confirm the sanitisation was complete. No certificate is issued unless verification passes. A failed verification triggers an automatic re-wipe and alert.
Operator Experience
We obsessed over the operator experience. Most data sanitisation tools look and feel like compliance teams built them. The UIs are dense, the workflows are confusing, and the error messages read like legal briefs.
Slate's touchscreen interface is designed for the person doing the work, often an IT support technician, a warehouse operator, or a volunteer at a device recycling charity. Big touch targets. Clear status indicators (colour-coded: blue for in progress, green for passed, red for failed). Plain-English confirmations at every step.
The NFC badge tap for authentication means operators don't need to type passwords on a touchscreen. The barcode scanner links the physical asset tag to the digital record without manual data entry. The thermal printer sticks a label on the drive the moment it passes, with a QR code that links directly to the certificate in Slate Cloud.
The full workflow (badge tap, connect drive, scan asset tag, confirm wipe, wait, print label) takes under 90 seconds for a typical NVMe SSD including the verification pass.
Drive Connected
Auto-detect type, capacity, capabilities
NVMe SSD
Method
NVMe Format + Crypto Erase
Standard
NIST 800-88 Clear/Purge
Typical time
~15s / 256GB
SATA SSD
Method
ATA Secure Erase
Standard
NIST 800-88 Purge
Typical time
~45s / 256GB
HDD (magnetic)
Method
Multi-pass overwrite (1/3/7)
Standard
NIST 800-88 Clear
Typical time
~25 min / 1TB (3-pass)
Flash media
Method
Full overwrite + verify
Standard
NIST 800-88 Clear
Typical time
~30s / 128GB
Block-level Verification Pass
Every sector read back and verified · Certificate generated on pass · Failure triggers re-wipe
A Wipe in 80 Seconds
A typical sanitisation operation on the Appliance, a single 256GB NVMe SSD, runs from badge tap to printed label in about 80 seconds.
Operator taps NFC badge
Identity verified, session started
Drive connected, auto-detected
Samsung 970 EVO Plus, 256GB NVMe, M.2 2280
Asset tag scanned
Linked to CMDB record AST-2024-00847
Method selected: NVMe Format + Crypto Erase
Auto-selected based on drive capabilities
Sanitisation in progress
Cryptographic erase command issued
Verification pass running
Block-level read of entire drive, confirming zero state
PASS — Certificate generated
Certificate ID: SLT-2026-00392, SHA-256 signed
Label printed, cert uploaded
QR code links to Slate Cloud certificate
Slate Cloud
A certificate is only useful if you can find it three years later at audit time. Slate Cloud is a web portal that stores every sanitisation certificate in a centralised, searchable, tamper-evident ledger.
Every certificate is cryptographically signed at generation (SHA-256 hash + RSA-2048 signature) and stored in an append-only data structure. Certificates cannot be modified or deleted after creation. The integrity of the ledger is verifiable by any auditor with the public key.
For air-gapped environments, certificates are stored locally on the Appliance and exported via encrypted USB transfer. When the USB is connected to a network-accessible machine, certificates sync to Slate Cloud automatically. The chain of custody is maintained throughout. Every certificate includes the timestamp, operator ID, device details, method used, and verification result, regardless of how it reached the portal.
The portal provides fleet-wide visibility for compliance officers and IT managers: how many drives have been sanitised this quarter, by which operators, using which methods. Anomaly detection flags unusual patterns: a sudden spike in failed wipes, an operator sanitising drives outside business hours, a device serial number that appears twice.
Audit-ready report generation exports data in the formats that NIST, ISM, and ASD assessors expect. No manual compilation, no spreadsheet wrangling. Click, download, hand to auditor.
The portal also exposes a REST API for integration with existing ITSM and CMDB platforms: ServiceNow, Jira Service Management, Freshservice. When a laptop is flagged for decommission in your ITSM, the sanitisation status can be tracked and verified programmatically without logging into a separate portal.
Wipe completes
Certificate generated locally
Crypto-signed
SHA-256 + RSA-2048 signature
Upload to Slate Cloud
Or queue for USB sync (air-gapped)
Portal stores cert
Append-only, tamper-evident ledger
Certificate Search
Find any cert by serial, asset tag, operator, or date range
Fleet Dashboard
Organisation-wide sanitisation activity at a glance
Compliance Reports
Audit-ready exports for NIST, ISM, ASD assessors
Role-Based Access
Operators, compliance officers, auditors — each sees what they need
API Access
Integrate with ITSM, CMDB, and asset management systems
Anomaly Alerts
Flagged: failed wipes, unsigned certs, unusual patterns
Compliance Coverage
Slate was designed against the standards from the start, not retrofitted for compliance after the fact. Every sanitisation method, every logging decision, every certificate field exists because a standard requires it.
| Standard | Scope | Slate Coverage | Status |
|---|---|---|---|
| NIST 800-88 Rev 1 | US federal media sanitisation | Clear, Purge, and Destroy (with evidence) | |
| ISM (Australian Gov) | Information Security Manual controls | Media sanitisation controls, audit trails, operator accountability | |
| ASD Media Guidelines | ASD media destruction & sanitisation | Method selection per classification level, verification passes | |
| DoD 5220.22-M | US DoD clearing & sanitisation | 3-pass and 7-pass overwrite methods available | |
| HB171 | Australian Govt ICT media handling | End-to-end chain of custody, certificate management | |
| ISO 27001 | ISMS asset disposal (A.8.3.2) | Auditable sanitisation records, tamper-evident logs |
Results
Slate is in production use across defence contractors, government agencies, and enterprise IT departments in Australia. The Appliance runs in IT disposal rooms, security cages, and warehouse loading docks. Slate Boot runs across end-of-lease laptop fleets at companies that process thousands of device returns per quarter.
Early adopters report an 80% reduction in per-drive sanitisation cost compared to external vendors. More importantly, they now have complete traceability: every drive, every wipe, every certificate, searchable and auditable. Several organisations have used Slate Cloud reports to pass compliance audits that previously required weeks of manual evidence compilation.
One defence contractor told us their previous process involved boxing up drives, couriering them to a vendor, waiting two weeks for certificates, and manually entering the results into a spreadsheet. With Slate, the same drives are sanitised on-site in an afternoon, and the certificates are in the portal before the operator finishes their shift.
The air-gapped deployment model has been particularly well-received in defence environments. The ability to operate with zero network connectivity, and sync certificates later via encrypted USB, solves a problem that no other product in the market addresses well.
We're currently developing Slate Destroy, an extension for physical destruction verification. A camera module photographs the destroyed media, generates an evidence package, and links it to the same certificate chain, closing the last gap in the audit trail for media classified at levels that require physical destruction.
Technology Stack
Appliance
- RK3588 SoC (custom Linux)
- Yocto-based embedded OS
- Qt6 touchscreen UI
- SQLite local cert store
Boot Image
- Custom Linux (x86_64)
- PXE + USB boot
- Text UI + web dashboard
- Network cert upload
Sanitisation Engine
- ATA Secure Erase
- NVMe Format (crypto)
- Multi-pass overwrite
- Block-level verification
Slate Cloud
- Next.js + TypeScript
- PostgreSQL (Neon)
- RSA-2048 cert signing
- REST API + webhooks